What Is Project Cheyenne?
Designed as a last line of defense
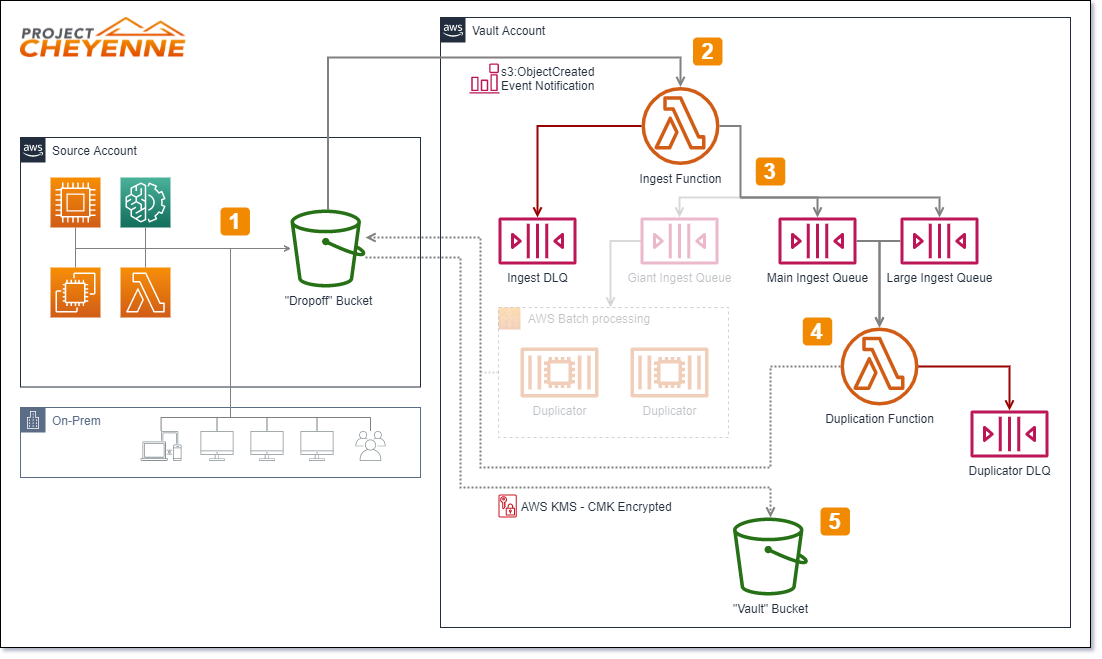
Today, more than ever, securely backing up your information / data / files is critical to maintain your business or organization. With ransomware attacks popping up daily, our team wanted to create an elegant solution that would be resistant to ransomware attacks. The one-way strategy ensures that if your primary system was attacked or compromised, the attacker or attacking malware would not be able to manipulate your backups. Similarly, for personal use, regular people are under identity theft and ransomware attacks on a daily basis and therefore you could benefit from a secure backup strategy.
-
Securely back up Your Company's Data
A one-way, cloud-enabled, secure backup solution for your personal or business use. -
Ransomware-Resistant Backup Storage Solution
The most critical dependency to recover from a ransomware attack is to have good backups. In many cases, the backup systems reside on the same networks that are compromised by ransomware. This leads to infection of the backups and in many cases, the backups become encrypted and inaccessible.
Cheyenne provides a one-way, version-controlled backup solution that prevents infection of backups and isolation from infiltration of hackers that leverage the compromise to install persistent threats. If you suffer from an attack, “break the glass” and know you can pull back from your Cheyenne vault to get your company back online. -
Easily Retrieve Data
Backups exist in S3 Cloud storage which can copy backups to your on premise or cloud solution.